
Physical mailing, old age isn’t it? Well, we’ve not come so from the time when physical mailing was the only plausible option for big sized confidential data. Subsequent data forgery is nothing but an extension by technology to technology. This called on technology to come up with something that could act as a solution to this problem of data forgery while transferring data online. Solon Li, The CEO of Authpaper Delivery has initialized such a platform to guard your data and store it on the platform through end-to-end encryption. To make sure that data is accessible to the recipient only, Authpaper ensures that-
There is no need for senders to stay online when recipients are about to receive the data. The platform rewards (stamps) peers for helping in data delivery to the recipient. This rewarding methodology encourages users towards the platform and send the data that is not accessible, increasing data delivery speed. This is based on a custom built blockchain to ensure that it’s completely decentralized, and there is no single authority.
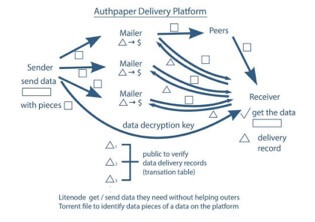
Fig. Authpaper Delivery workflow structure
Encryption (symmetric and asymmetric algorithms)
Confidentiality is reached at a point where all the data is transformed to a state which has been deployed to nothingness. This transformation process is known as encryption. To read back the data, entities use some private information (keys) to convert the void data (encrypted data) back to its original state. This is called decryption.
There are mainly two kinds of algorithms providing encryption,
2. Asymmetric key algorithm– These are commonly referred to as public-key algorithms because there are two mathematically associated keys known as public and private keys involved. The combination of a public and private key is called a key pair. The owner never discloses the private key. The public key is distributed among the public and is accessible to everyone. The private key cannot be deduced from the public key. The public key is used to encrypt the data in a way that only the party with private key can decrypt it. When a party would like to send a data to another party, the party gets the public key from the recipient and encrypt the data. As private key is known to the recipient only, so only the recipient can read the data. Unlike symmetric key algorithms, asymmetric-key algorithms allow multiple parties to send encrypted data to the same recipient using the same key pair. Compromising any entity does not compromise the communications of other entities. However, symmetric algorithms are still used in encryption as they are much faster.
Public and US National Institute of Standards and Technology (NIST) have performed uncompromising security testing and analysis before their approval on any such algorithm, to assure satisfactory security by the algorithm. Authpaper Delivery platform as recommended by NIST for use beyond 2030, will use Advanced Encryption Standard with 256-bit keys for symmetric encryption (AES 256) and Elliptic-curve cryptography with 521-bit keys for digital signature and key exchange.
Disclaimer: This is a paid press release. KryptoMoney does not endorse and is not responsible for or liable for any content, accuracy, quality, advertising, products or other materials on this page. Readers should do their own research before taking any actions related to the company. KryptoMoney is not responsible, directly or indirectly, for any damage or loss caused or alleged to be caused by or in connection with the use of or reliance on any content, goods or services mentioned in the press release.
Keep in mind that we may receive commissions when you click our links and make purchases. However, this does not impact our reviews and comparisons. We try our best to keep things fair and balanced, in order to help you make the best choice for you.