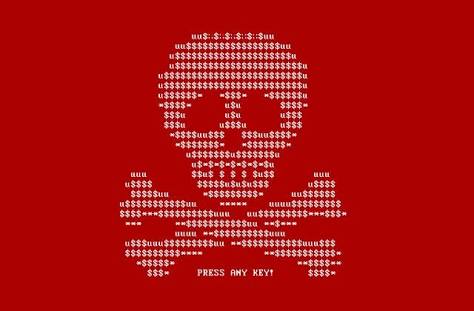
A computer virus of the ransomware type, which encrypts the contents of a computer to render it unusable until payment of a ransom, paralyzes the operation of many companies in the world on Tuesday 27 June 2017.
Ukraine is the most affected country, but companies like Saint-Gobain or the Russian oil giant Rosneft are also concerned.
The first alerts were given in Ukraine, the country most severely affected, in the early afternoon. The operation of several banks, the subway, several administrations and the energy operator of the Kiev region is largely disrupted. The Ukrainian Deputy Prime Minister’s computer was himself hit, he said on Facebook.
The Ukrainian Prime Minister described the episode as “unprecedented,” adding that “the vital systems [of the country] have not been affected.” However, the automated radiation control system at the Chernobyl nuclear power plant has been affected by the virus, forcing the supervisory authority to return to manual controls.
Elsewhere in the world, several major companies, including the giant Saint-Gobain building, the Russian oil tanker Rosneft, the British advertising group WPP, and the Danish heavyweight Maersk have confirmed they are victims of “computer attacks” In part or totally their services. The Petya virus is indeed the MBR, the part of the hard drive that contains the software used to start the computer, making it totally unusable, where most of the usual ransomwares “content” themselves with blocking access to personal documents .
US and British companies have also been hit by an attack. Pharmaceuticals giant Merck said on Twitter that its computer network was targeted by the “global” attack, and according to the specialized Motherboard site, offices of the law firm DLA Piper have also suffered attacks. According to an initial analysis carried out by the specialist Kaspersky, 60% of the infected computers are in Ukraine, and 30% in Russia.
The virus seems to be a variant of a ransomware appeared in 2016, named Petya, according to initial findings of computer security specialists. “We are currently seeing several thousand attempts at infection, a pace comparable to the early hours of deployment of Wannacry [a virus that had spread dramatically on May 19],” said Costin Raiu, Kasperksy, questioned by Forbes.
According to several computer security companies, this strain of Petya uses EternalBlue, a tool derived from the NSA, the powerful American intelligence agency. It was he who was already responsible for the flash propagation of WannaCry in May. The flaw that it uses is however corrected since April by Microsoft, which means that the machines affected by this last variant of Petya were probably not updated.
In France a cyber-security provider has come to the rescue of the affected users and have made public notice on their website.
How to avoid being infected by Petya?
It is still unclear how the Petya virus has spread, but ransomware usually spreads via e-mail attachments before spreading on the local network. It is strongly recommended that you do not open attachments from e-mails you do not know the recipient, and more generally, apply Windows security updates if they are not automatic. It is also prudent to make backups on media that are not connected to the Internet, such as external hard drives.
This article was contributed by Author Bhargavi Sayee.
Keep in mind that we may receive commissions when you click our links and make purchases. However, this does not impact our reviews and comparisons. We try our best to keep things fair and balanced, in order to help you make the best choice for you.